Insights on the Super Micro Story and China Hack.
| Corvalent
Security First: Insights on the Super Micro Story
Corvalent takes security seriously – as a manufacturer of high performance computing systems, it’s an essential part of what we do. This has always been our position, and should be a given for any embedded OEM or ODM that plays a role in the supply chain of critical system development. Adhering to security standards and well-established design protocols is more important than ever, protecting the connected systems that literally run the world and remaining vigilant against constant and evolving cyber threats. In this landscape, a story like Bloomberg’s report on the hacking of Super Micro hardware raises grave concerns. At the same time, we need to take a hard look at the realities of hardware hacking and gauge our response on a real-world understanding of its impact and limitations.
What Happened at Super Micro?
The team at Corvalent has been closely watching the Super Micro chip situation. According to all information contained in the Bloomberg article, and subsequent reports from additional news sources, we saw the issue described in several ways:
- A small, powerful chip, was somehow installed by Super Micro’s Chinese subcontractors without their knowledge
- Malware or modified software replaced the original code in the BMC chip, on their server boards only
- Modifications were made to the RJ45 connector and associated internal components
These are all very different and complex forms of hacking, and the specific detail of the Super Micro hacking is not entirely clear.
Do Corvalent Customers Need to Worry?
Some of our customers have already asked us about the risk or possibility that Corvalent products could have been affected by the same kind of hardware bug. The answer is no, we are not an attractive target for an expensive and complex attack.
Corvalent has been in business for decades, with a business model featuring high mix industrial use and customized boards and/or systems, from hardware to firmware and software. Blend this with our track record of longevity, our long term relationships with trusted vendors and suppliers, and the fact that even similar boards produced by Corvalent end up in completely different areas of the industry, running completely different types of operating systems and application software: the result is we believe Corvalent to be in a very low risk bracket and a highly unlikely target for hardware hacking.
What is Corvalent’s Insight on Hardware Hacking?
“It is our technical opinion that modifications of hardware, firmware and/or software are all possible ways to interfere with the normal operation of boards. Each of them has advantages and disadvantages, including technical complexity, ease of detection, and cost of implementation,” said Martin Rudloff, Corvalent’s CTO. “Typically this means that for someone to deploy an attack of the scope reported by Bloomberg in its Super Micro feature, the target must be specific and worthwhile in order to justify the high cost involved. Targeting only one or a few major companies would also minimize the risk of discovery.”
“Without deeper knowledge of the hardware and the software running on a server, information gathered from it may not allow a thief to decode or understand what the data means. And without knowing the end users’ security measures, we find it unlikely that the information could be forwarded to an external recipient,” added Rudloff.
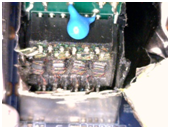
Curiosity kicked in when we were discussing the level of difficulty in modifying the RJ45, so we decided to open one and check it out firsthand. As you can see below, it is very hard to open the metal enclosure without damaging it. The interior is fully packed, leaving little space to add additional circuitry. A fully assembled modified unit would probably be a better choice, but would involve the highly sophisticated effort of tapping into the supply chain and replacing the original parts with counterfeits.

Should we Question Such a Significant Story?
Bloomberg is a trusted news source with impeccable standards for truth and accuracy in reporting. Even so, it is possible that the story is incorrect. Sources provided data they understood to be accurate and truthful based on reports seen by them only; however, these were not shared with Bloomberg directly. There are technical inconsistencies to consider as well.
- It should be possible to detect oddities in network traffic coming from a BMC behaving in unexpected ways. Alterations to the kernel and software stack should also set off alarms during or after system boot.
- The chip pictured in the Bloomberg story fits on the tip of a pencil, yet it purportedly holds enough data to replace the data extracted from the BMC, alter the existing OS, and implement backdoor system access. This means the chip must either be larger than pictured or is using new lithography.
- Why go to the trouble of placing a new chip on the board instead of a backdoor version of one already certified as part of the design?
Strong and specific denials by Amazon and Apple – different from the usual ‘we do not discuss issues of security as a matter of policy’– further stress the story’s validity.
What’s Next?
Corvalent will continue to follow all updates available on the situation, and has already contacted suppliers and partners to raise awareness. Our team is at the ready to answer your questions, and assure you our proven security policies and standards remain a priority at every level of system design and development.
If you have any questions regarding our products and production process, please feel free to contact our sales executives at 888.776.7896 or contact us here https://corvalent.com/support/
About the Author
